Microsoft Fights Back on Phishing Scam

Hackers Infect UCSF Medical Research and School Pays $1.4 Million to Recover it
July 1, 2020
Thieves Are Using Indoor Security Cameras to Their Advantage
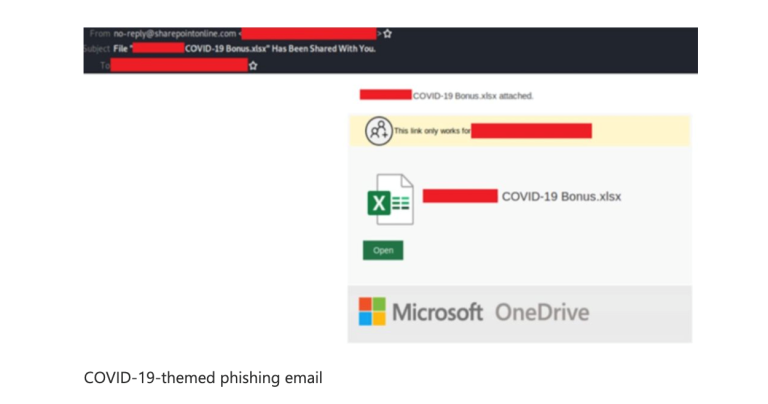
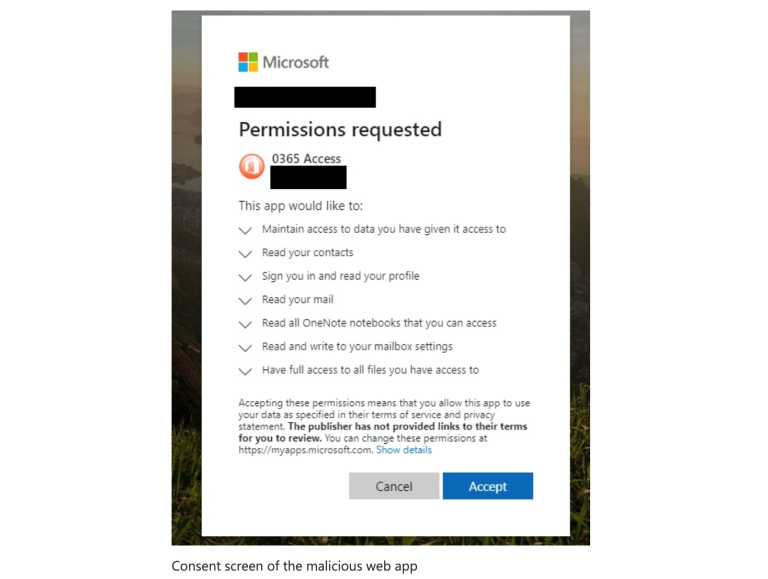
July 10, 2020If you get an email offering a “COVID-19 bonus” beware! Microsoft is warning it’s users that a pair of hackers has been deceiving business employees into turning over their access to their email accounts. The unfortunate victims who clicked on the link were prompted to grant access permissions to a malicious web application.
Earlier this week, Microsoft described the phishing attacks, which have been attempting to take over Microsoft Office 365 accounts from business users across 62 different countries.
The good news is that Microsoft is fighting back. A U.S. District Court order has allowed Microsoft to take over control of key domains used by these cybercriminals who deployed the novel coronavirus-themed phishing campaign targeting Microsoft customers.
The sophisticated phishing campaign was designed to compromise thousands of Microsoft customer accounts and gain access to customer email, contact lists, sensitive documents and other personal information in an effort to exfiltrate information, re-direct wire transfers and launch further cybercrime from compromise accounts, according to a 27-page U.S. District Court complaint unsealed Tuesday.
“This unique civil case against COVID-19-themed BEC [business email compromise] attacks has allowed us to proactively disable key domains that are part of the criminals’ malicious infrastructure, which is a critical step in protecting our customers,” Burt wrote in a blog post Tuesday.
Microsoft has been quietly watching and investigating the hacking group’s phishing scams since December. The original messages used more generic business subject lines, such as “Q4 report — Dec 19.” But as Covid numbers grew and the pandemic escalated, the hackers began exploiting the Coronavirus frenzy to manipulate users into opening their malicious emails, including use of the term “COVID-19 bonus” on links or files attached to the emails. “
Microsoft has since shared that the pair of anonymous hackers directed millions of phishing emails at chief executives and senior managers in both the private and public sector.
The phishing scheme is yet another reminder to be on guard about suspicious third-party apps; if they ask for sensitive permissions, you may want to avoid installing them.
If you need assistance with Managed Cybersecurity Services contact DarkHound SecOps at [email protected] for more information.
Sources:
https://www.pcmag.com/news/hackers-try-to-phish-business-executives-with-covid-19-bonus-promise
https://www.infosecurity-magazine.com/news/microsoft-takedown-phishing/
https://www.crn.com/news/security/microsoft-seizes-domains-used-for-covid-19-themed-phishing
https://www.crn.com/news/security/nsa-sounds-alarm-on-severe-microsoft-windows-security-flaw
Image Source:




